Remote work has evolved as a permanent work model for most companies, even though the pandemic is mostly over. But, allowing employees to work remotely puts companies at significant risk of cyber attacks.
Since 2020, there has been exponential growth in cybercrime rates, and shortly cybercrime rates don’t seem to regress even a bit. Experts foresee that cybercrime rates will increase by 15 percent per year, and cybercrime damages will cost the world 10 trillion dollars annually by 2025.

This prediction indicates that companies of all sizes can face cyber attacks anytime. When companies don’t implement adequate security measures to combat cyber attacks, the confidential data they store can be stolen. Data breaches bring serious consequences that no company desires. Securing remote access of your company is vital these days, and providing secure remote access to your employees isn’t as hard as most people think.
There are many ways to secure remote access to your employees when they work remotely from anywhere in the world. Throughout this article, we will analyze the top 5 tips for remote access that will help you build a good cyber security posture against cyber attacks.
1- Use A Good VPN
Virtual Private Networks (VPNs) have been reliable remote access solutions for over twenty years. In an era of remote work, using a good VPN solution can be critical for your company’s future. VPNs function by building private tunnels between employees and company resources over the internet. This way, employees can securely access what they need without interruptions.
The presence of VPNs can establish your company’s online privacy and anonymity, and they will disguise your internal traffic from prying eyes. Also, VPNs can strengthen data security as these use end-to-end data encryption, making each data transfer indecipherable for everyone who isn’t authorized. Shortly, employing a good VPN solution is the simplest and cheapest way to accomplish secure remote access.
2- Put Solid Password Policies
Putting solid password policies in place is necessary because employees generally set up weak passwords, which can quickly be compromised. For this reason, you need to clarify the requirements for strong passwords and advise them to set up unique, complex, and long passwords that don’t include personal information. Also, your employees need to change their passwords regularly.

So, in your password policy, you can put a 90 or 120 days rule that will oblige them to change their password once they exceed this time period. On top of these, you can require your employees to use password manager tools that will help them generate unique and strong passwords.
3- Utilize Multi-Factor Authentication (MFA) Tools
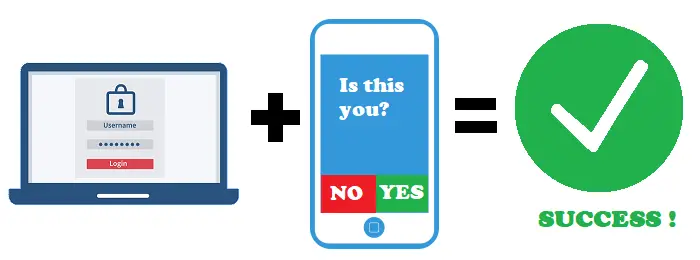
On top of enforcing a strong password policy, you need to utilize multi-factor authentication (MFA) tools. These tools put an extra layer of security to the access process and strengthen authentication procedures. MFA tools demand users verify their identities in two or more ways.
Authentication methods include in-app approvals, one-time passwords, biometrics, security keys, tokens, etc. Every MFA tool uses combination authentication methods. For example, an MFA tool can first require login credentials, then send OTPs and demand biometric authentication like fingerprints. After providing all authentication factors to the mechanism, an employee can access the company’s applications and data. MFA tools are critical for remote access, and they eliminate the security risks related to leaked and compromised passwords.
4- Adopt Identity Access Management (IAM) Solutions
Adopting Identity Access Management (IAM) solutions is one of the great ways to establish secure remote access. IAM solutions refer to assigning access privileges to employees and authenticating their identities via MFA, biometrics, and single sign-on (SSO) tools. While using IAM tools, your IT admins can set access privileges for every employee, device, or application. Simply, these tools first authenticate employees’ identities, then grant access to the company’s networks and resources in accordance with their access privileges.
This way, you can limit employees’ access scope and restrict access to certain areas that have confidential data. Using IAM tools is best for mitigating internal and external security risks.
5- Consider Secure Access Service Edge (SASE) Solutions
Secure Access Service Edge (SASE) is an all-in-one solution that interconnects networking and security features and functions as a cloud-native service. This architecture’s components are SD-WAN as service, Firewall as Service (FWaaS), Secure Web Gateway (SGW), Zero Trust Network Access (ZTNA), and Cloud Access Security Broker (CASB). Secure remote access is accomplished via SD-WAN.
When an employee wants to connect a company’s resources and data, SD-WAN establishes direct and secure connections by selecting the best routes. The remaining components of SASE have enhanced security features like network segmentation, malware detection, threat prevention, URL filtering, etc. If you want to create an aligned and advanced security setup, SASE is the way to go. But, this architecture requires time, expertise, and money to function fully. That’s why it might not be the best fit for small organizations.
Last Remarks
In a century of remote work, providing secure remote access to employees is vital for companies of all sizes. These days organizations face the greatest security risks of all time. To protect your company and employees against cyber attacks, you need to implement robust security tools, measures, and policies.






