In this guide, we will learn how to set up an IPsec site-to-site VPN between Fortigate and SonicWall devices. In this way, we can use both devices to connect two branches or locations. I assume that there are two different IP subnets available at both locations.
This demonstration was done with the FortiOS 5.2 and SonicOS 6.1.2 versions. While reading this guide, there could be a new OS from both vendors that will have different GUI and screens. But fundamentally, the main steps remain the same. You will find similar settings/screens with the new OS as well. Few online guides and Q&A’s helped me to set up the IPsec Site to Site VPN between these two devices successfully. Luckily both locations had static (fixed) public internet IPs. If that is not the case for you, you need to use dynamic DNS to resolve the IPs and make the connection. But it is always recommended to have static IP at your head office which acts as a hub in the VPN network.
I explained the steps clearly without complicating the below example. To configure DynDNS in FortiOS 5.0 and later versions, please refer to this guide at Sysprobs. To configure DynDNS in Sonicwall, this post would be helpful. I did this demonstration of setting up a VPN between Sonicwall and Fortigate on the Sonicwall NSA 2600 model and Fortigate 110C hardware devices.
Read Also: How to change the switch mode to interface mode in FortiOS
The Scenario
The head office has IP subnet 10.10.11.0/24 with Fortigate device and the branch has 192.168.100.0/24 with Sonicwall. So the branch computers with IP range 192.168.100.0/24 will access servers in 10.10.11.0/24 and vice versa. The below basic diagram can explain more to understand the VPN settings and configurations in the next steps.
Steps to Configure VPN Between Sonicwall and Fortigate
Let’s start with Fortigate. I assume you already have some basic knowledge of Fortigate and SonicWALL VPN settings. As I mentioned earlier, you will see completely different GUI/screens on your devices depending on the OS version you use.
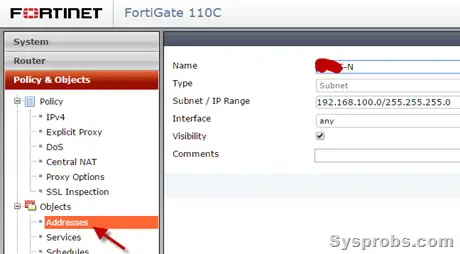
1) Make sure that the head office and branch network addresses are created in the Fortigate objects area. Here is how I created the branch network object.
2) Create an IPsec VPN tunnel and select ‘Custom VPN Tunnel’ with a name for the VPN tunnel.
Select the destination (in this case, it is SonicWALL) IP or DynDNS name. Select the WAN interface which is connected to the internet for VPN connectivity, WAN1 is for me. Other settings remain the same as shown below.
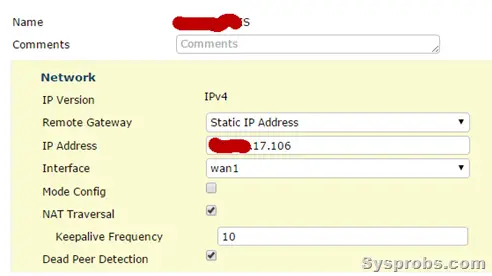 3) Enter the preshared key (like a password) which needs to be entered in the Sonicwall device to create the site to site VPN between these two devices.
3) Enter the preshared key (like a password) which needs to be entered in the Sonicwall device to create the site to site VPN between these two devices.
Select the ‘Main’ mode for VPN connectivity.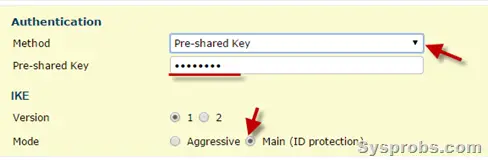 4) Phase 1 proposal is something important.
4) Phase 1 proposal is something important.
By default, FortiOS comes with few encryptions. Remove all encryption and authentication settings. Select only 3DES and SHA1 as shown below.
Then select only DH Group 2. Key Lifetime set to 28800. We will be using these exact settings in the Sonicwall firewall.
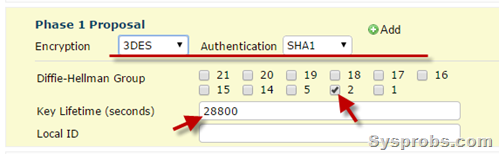 5) Phase 2 settings are also important while setting up the VPN.
5) Phase 2 settings are also important while setting up the VPN.
Select the Local network and Remote address (the branch network address we created in step 1). The encryption settings should be only 3DES and SHA1. Untick ‘Enable Replay Detection’ and ‘PFS’ as below. Make sure other settings remain the same.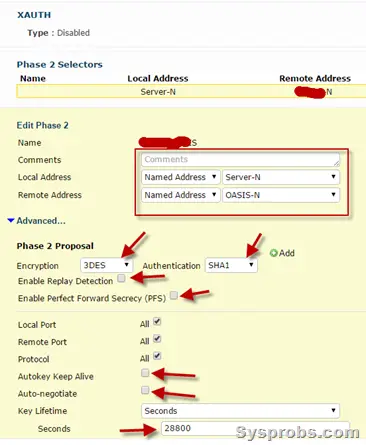 Basically, we have created the site to site VPN tunnel in the Fortigate device. Since I’m not mentioning all steps here, we have to create a firewall policy for incoming and outgoing traffic through a VPN tunnel. Also, route entry is essential to route the branch network traffic from the head office network through the VPN tunnel.
Basically, we have created the site to site VPN tunnel in the Fortigate device. Since I’m not mentioning all steps here, we have to create a firewall policy for incoming and outgoing traffic through a VPN tunnel. Also, route entry is essential to route the branch network traffic from the head office network through the VPN tunnel.
SonicWall Setup:
To be honest, I’m new to SonicWall. The information I gathered online helped me set up the Site to Site VPN correctly with Fortigate.
6) Create address objects for head office and local network.
It can be created under ‘Network’ and ‘Address Objects’. Here is the example of the head office network address object I created. When you create the address object for a remote location (connected to the Fortigate network) which will be connecting through a VPN tunnel, select ‘VPN’ in Zone Assignment. Other local internal networks will be assigned to the ‘LAN’ zone.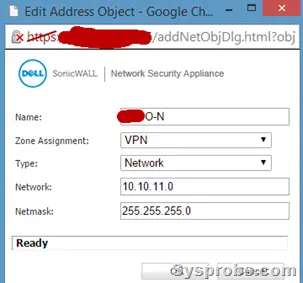 7) Create a VPN tunnel with the following settings.
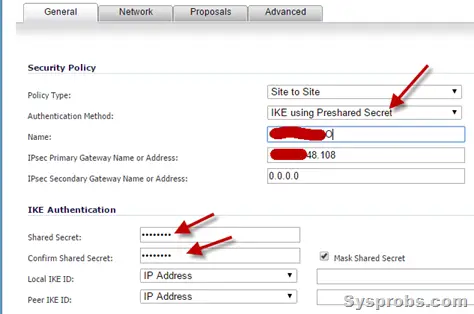
7) Create a VPN tunnel with the following settings.
Important settings are; Authentication method should be ‘IKE using Preshared secret’, IP address of Fortigate public interface and the preshared secret key which we entered in step 3 in Fortigate VPN settings. Leave the other settings as below.
 8) Click on the ‘Network’ tab and set the settings as below.
8) Click on the ‘Network’ tab and set the settings as below.
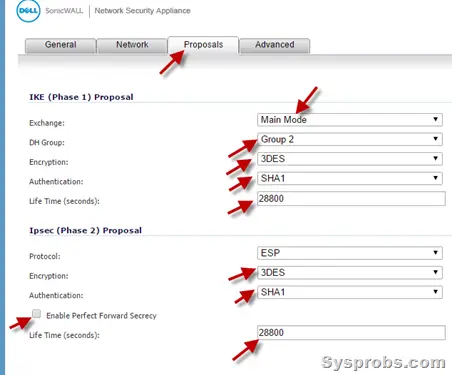
Choose the local network and remote (head office) network addresses which we created in Step 6.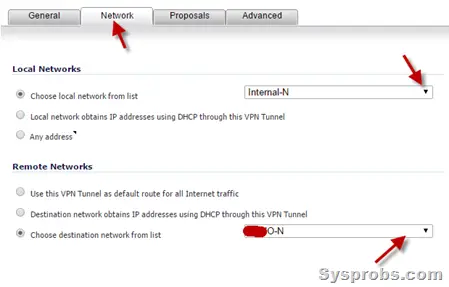 9) Proposals tab in the SonicWall VPN setting is essential to set up an IPsec VPN tunnel with the FortiGate device.
9) Proposals tab in the SonicWall VPN setting is essential to set up an IPsec VPN tunnel with the FortiGate device.
Make sure to set the same settings as we did in the Fortigate device.
For example, the VPN mode is ‘Main Mode’, DH Group is 2 and other all settings should match with the proposal settings we did in the Fortigate VPN tunnel settings.
Make sure to untick ‘Enable Perfect Forward Secrecy’ as below.
10) In the Advanced tab, tick the ‘Enable Keep Alive’ option.
 With the above steps, we havesuccessfully set up the VPN in SonicWall and Fortigate. Luckily, we do not need to create any separate firewall policies or route entries in SonicWall like Fortigate. Once the VPN tunnel is up, the traffic will flow through this IPsec site to the site VPN tunnel between two locations.
With the above steps, we havesuccessfully set up the VPN in SonicWall and Fortigate. Luckily, we do not need to create any separate firewall policies or route entries in SonicWall like Fortigate. Once the VPN tunnel is up, the traffic will flow through this IPsec site to the site VPN tunnel between two locations.
Hope this step by step guide is helpful in set up a VPN between SonicWall and Fortigate with the latest OS versions of respective devices. Do share whether this guide is helpful or any other better alternative ways to make the VPN setup.







Hi,
Thanks for this post. Very great one.
I followed your instructions and created 3 IPsec tunnels. All 3 are up, but the traffic goes up and down on one tunnel “only”. To reestablish the connection, I have to click on “renegotiate” on the sonicwall, then after 5 minutes the traffic goes down.
Can you please help me?
Thanks in advance